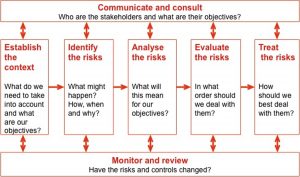
Philosophy of Security, Part 5 – Risk Management – The Process At in the previous parts of this security series we have look at what it is , why we do it, and at some psychological factors such that affect the way we do it. Significantly, in part 4, I noted that: … research has …
Category: ICT Security
May 29
Risk Rating and Treatments
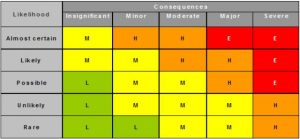
Philosophy of Security, part 9 – Risk Management – Risk Rating and Treatments So far we have discussed how to quantify the likelihood of, and the impact arising form an event. In this part I would like to pull it all together and look at how we rate and prioritise risks and also look at …
Jun 26
Consequences and “Risk Appetite”
Philosophy of Security, part 8 – Risk Management – Consequences and “Risk Appetite” So far, looking back at security discussion series in part 7 we took a side trip to explore a different way of looking at vulnerabilities called the Attack Surface. Earlier, in part 5, we have looked at the overall Risk Management process …
Jun 25
What is an “attack surface”?
Philosophy of Security, part 7 – Risk Management – What is and “attack surface”? In part 6 we have discussed threats and vulnerabilities, their relationship with each other and with overall idea of risk. This post is a small side trip to explore a related concept. There is a related concept, that is often used …
Jun 25
Risk Management – Threats and Vulnerabilities
Philosophy of Security, part 6 – Risk Management – Risks: Threats and Vulnerabilities In previous part, Part 5 of this series we discussed the general approaches to Risk Management. In this part I wish to take a closer look at the heart, and technically, the most difficult part of the process – Risk Analysis – …
Jun 13
Why do we do security?
Philosophy of Security, Part 2 – Why do we do “security”? In Part 1 of this series we have looked at a high level concept of what it is that we are dealing when when we talk about security. No matter what else you might think on this topic, there is one fact about security …